Surplus Liquidation Solutions, LLC Service Center
Utilize Our Service Center When Selling Your Surplus Equipment
Secure Operations & Compliance-Focused Asset Processing
Controlled Facility & Risk Protection
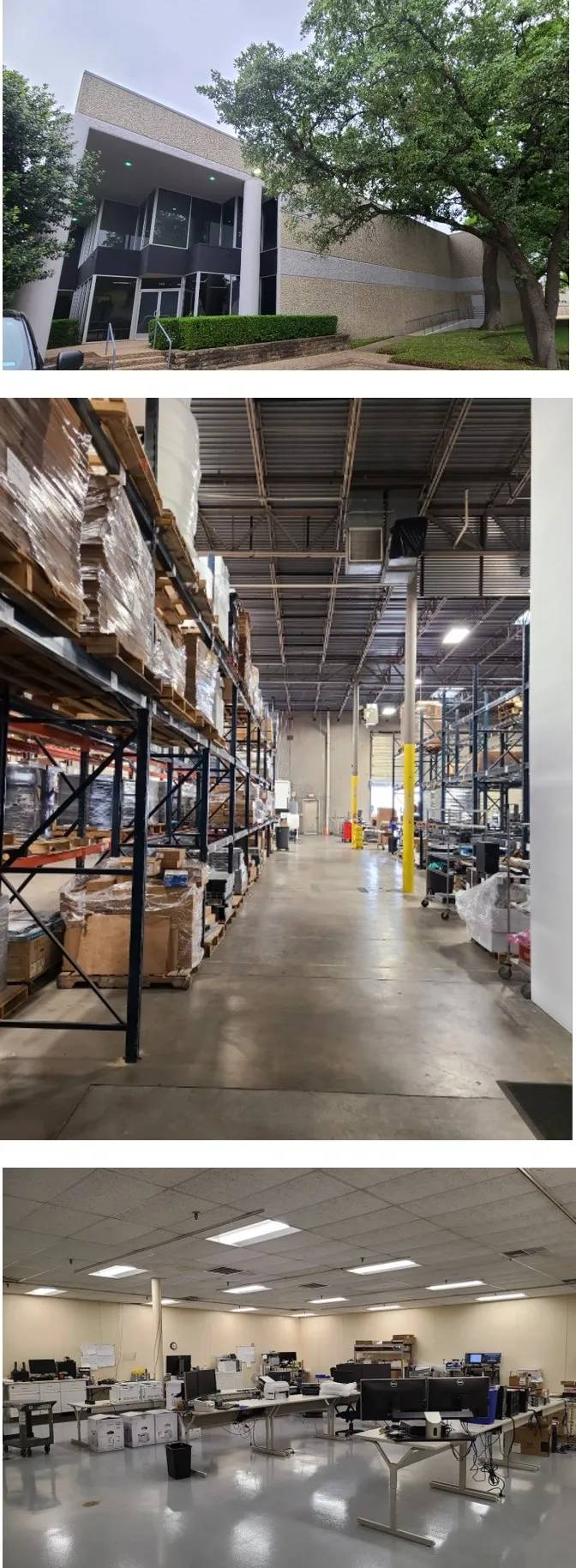
SLS operates from a 25,000-square-foot secured facility in Carrollton, Texas, located near DFW International Airport. Our operations are fully bonded and insured, supporting enterprise risk management and third-party oversight requirements.
Chain of Custody & Asset Accountability
All incoming client assets are formally received, audited, and logged into our inventory management system prior to processing. Each device is tracked through every stage of handling, servicing, and final disposition.
Detailed reporting—including device and storage media serial numbers—is maintained to support audit readiness and internal compliance requirements. Clients are provided visibility into asset status throughout the project lifecycle.
Data Security & Onsite Processing Controls
All data sanitization and destruction services are performed onsite within secured-access technical labs. Processing workflows are structured to reduce risk of data exposure and unauthorized handling.
Services may include:
- Certified data erasure using approved software tools
- Storage media removal and documented destruction
- Degaussing and physical shredding where required
- Secure return of storage devices when requested
Certificates of Data Destruction and detailed asset records are provided to support regulatory, legal, and internal audit standards.
Secure Handling & Release Procedures
Assets are stored, processed, and staged within controlled areas of our facility. Upon sale, equipment is professionally prepared for shipment, with documented release procedures to maintain chain-of-custody integrity through final transfer.
Designed for Regulated Environments
SLS supports organizations with heightened governance requirements, including financial institutions, healthcare entities, and other regulated enterprises. Our processes are structured to align with internal security policies, risk management standards, and compliance expectations.